How is this a backdoor if it requires being able to install custom PAM modules???
First, you break into the house, then you install an invisible backdoor, and then you can come and go freely.
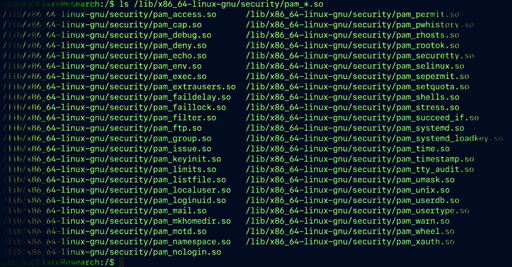
It’s a “post-exploit” tool. It’s the persistent backdoor you install after you break in. It survives reboots, unlike most exploits.
It feels like a terrible horrible no good bad month for Linux :(
These kind of exploits have always been common. The only thing that changed is people talking about them.
I fell it’s going to be a bad couple of months for everybody, not just Linux. It’s just with open source, it’s easier for the LLMs to find things that have been missed. And more open when they do because you can see the bug reports.
How many of these security news stories are largely exaggerated by Redmond and its affiliated outlets?
I think it’s best to read the actual docs published by the research when available. News tells some, but I have seen it sensationalized a few times, where it only affects x kernel with y module before update z.
That being said, these are seemingly getting more and more frequent as previously noted.
If it was backdoor that means someone created it maliciously or it is bug?
It is a tool to establish persistente after the server is already hacked. This isn’t a way to break into a server.